Madoka.exe: Difference between revisions
No edit summary |
mNo edit summary Tag: Manual revert |
||
| (54 intermediate revisions by 20 users not shown) | |||
| Line 1: | Line 1: | ||
{{ | {{#seo: | ||
[[ | |keywords="Madoka.exe, Madoka.exe application, Madoka virus, Madoka.exe screamer, Sadako virus, Madoka screamer, Madoka malware, Madoka screamer, Madoka screamer, Madoka.exe download" | ||
'' | }} | ||
{{Deleted}} | |||
{{Infobox | |||
|title = Madoka | |||
|image = Madoka.png | |||
|maker = Qiwen Lin | |||
|type = [[Application]] | |||
|date = 2001 | |||
|imagecaption = The '''Madoka.exe''' icon. | |||
}} | |||
'''Madoka.exe''', also known as the '''Ghost virus''' or the '''Sadako virus''' in Japan, was a Taiwanese [[screamer]] [[program]]. It is a variant of the Win32/FlaGhost malware. The original author is Qiwen Lin (林 啟文) and it was written in the [[wikipedia:Hot_Soup_Processor|Hot Soup Processor]] programming language. | |||
==Payload== | |||
[[Category:Applications]] | When the user runs the malware by executing the [[.exe]] directly, a picture of Madoka Ozawa, a Japanese adult actress, in full screen is displayed along with the "introduce dialogue" Chinese text showing line by line in the upper-left corner of the screen. However, a ghost version of the woman in the image will appear briefly along with a scream sound effect, before immediately returning to the original image. | ||
Before showing the initial payload, the malware will copy itself to the Windows directory as <code>ozawa.exe</code> and try to append itself to <code>win.ini</code> in order to auto start with the operating system. Judging from the decompiled source code, this only works on [[wikipedia:Windows 98|Windows 98]] and [[wikipedia:Windows ME|Windows ME]]. On [[wikipedia:Windows_XP|Windows XP]] or higher, there is no ''Run'' section in <code>win.ini</code> and the malware will not work apart from the initial payload. | |||
If the malware is launched from the system directory as <code>ozawa.exe</code>, either from auto start or double clicking manually in the system directory, it will enter "reside mode" without showing the initial payload with the normal woman picture. Instead, it runs in background. It will then show the screamer image along with the scream sound effect indefinitely in the following intervals: 3 minutes, 10 minutes, 30 minutes, 60 minutes, and then subsequently every 60 minutes. | |||
If the user executes the original .exe once again after infection, the normal woman picture and the "meet-again dialogue" text will be shown and there is no screamer picture. | |||
The program also records the number of executions of the original .exe (not the one in system directory) in <code>win.ini</code>. If it is run over 5 times, the malware will show the "bye dialogue" with the normal woman picture, then uninstall itself. | |||
== Dialogue== | |||
<tabber> | |||
Introduce Dialogue= | |||
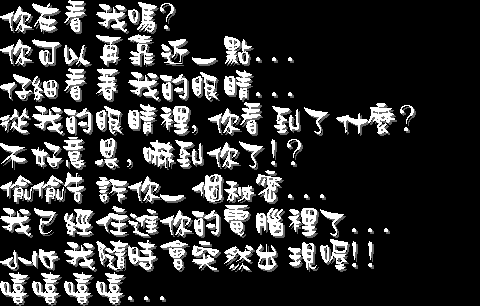
[[File:Madoka mess1.bmp|none]] | |||
Are you looking at me? | |||
You can get closer... | |||
And look into my eyes... | |||
What can you see in my eyes? | |||
'''<Screamer>''' | |||
Ah, sorry for scaring you. | |||
I'm gonna tell you a secret... | |||
I've already dwelled in your computer... | |||
Beware that I may appear anytime! | |||
Hehehe... | |||
|-|Meet-again Dialogue= | |||
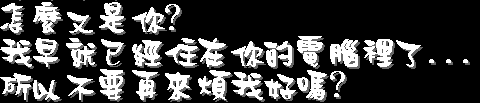
[[File:Madoka mess2.bmp|none]] | |||
Why it's you again? | |||
I've already living in your computer... | |||
Could you please stop bothering me? | |||
|-|Bye Dialogue= | |||
[[File:Madoka mess3.bmp|none]] | |||
You are so annoying! | |||
I'm not gonna living in your computer anymore... | |||
Bye... | |||
</tabber> | |||
==Trivia== | |||
*The original EXE accepts arguments. The accepted arguments are shown below: | |||
** '''/inst''': Install to system directory silently, without the initial payload. | |||
**'''/unst''': Uninstall the installation | |||
**'''/ver''': Show an about dialog message box with version | |||
* According to the decompiled source code, holding down F10 when double clicking the original EXE will cause the malware to decompile itself and unpack all the assets and codes. However, this behavior is tested not working on a WinXP virtual machine. | |||
==Link== | |||
<u>NOTE</u>: The following application contains a [[screamer]]! | |||
*web.archive.org/web/20041106190224/geocities.co.jp/SiliconValley-Oakland/8358/mysoft/files/madoka08.zip | |||
*files.screamer.wiki/other/madoka08.zip | |||
*'''Author's homepage''': web.archive.org/web/20040806024306/geocities.co.jp:80/SiliconValley-Oakland/8358/mysoft/mysoft.html | |||
*'''Showcase''': youtube.com/watch?v=COIEKlgnDm4 | |||
==See also== | |||
*[[McDonalds.exe]] | |||
*[[Happy Days.exe]] | |||
*[[Hikaru.exe]] | |||
{{Maliciousnav}} | |||
[[Category:Malware]][[Category:Applications]] | |||
[[Category:Other scary images]] | [[Category:Other scary images]] | ||
[[Category:Japan]] | |||
[[Category:Other makers]] | [[Category:Other makers]] | ||
[[Category:2001]] | [[Category:2001]] | ||
[[Category: | [[Category:Joke_screamers]] | ||
[[Category:Malicious_scripts]] | |||
{{Comments}} | |||
Latest revision as of 07:32, 17 June 2024
|
This page is about a screamer or shock site, whose original copy has been deleted. |
Madoka.exe, also known as the Ghost virus or the Sadako virus in Japan, was a Taiwanese screamer program. It is a variant of the Win32/FlaGhost malware. The original author is Qiwen Lin (林 啟文) and it was written in the Hot Soup Processor programming language.
Payload
When the user runs the malware by executing the .exe directly, a picture of Madoka Ozawa, a Japanese adult actress, in full screen is displayed along with the "introduce dialogue" Chinese text showing line by line in the upper-left corner of the screen. However, a ghost version of the woman in the image will appear briefly along with a scream sound effect, before immediately returning to the original image.
Before showing the initial payload, the malware will copy itself to the Windows directory as ozawa.exe and try to append itself to win.ini in order to auto start with the operating system. Judging from the decompiled source code, this only works on Windows 98 and Windows ME. On Windows XP or higher, there is no Run section in win.ini and the malware will not work apart from the initial payload.
If the malware is launched from the system directory as ozawa.exe, either from auto start or double clicking manually in the system directory, it will enter "reside mode" without showing the initial payload with the normal woman picture. Instead, it runs in background. It will then show the screamer image along with the scream sound effect indefinitely in the following intervals: 3 minutes, 10 minutes, 30 minutes, 60 minutes, and then subsequently every 60 minutes.
If the user executes the original .exe once again after infection, the normal woman picture and the "meet-again dialogue" text will be shown and there is no screamer picture.
The program also records the number of executions of the original .exe (not the one in system directory) in win.ini. If it is run over 5 times, the malware will show the "bye dialogue" with the normal woman picture, then uninstall itself.
Dialogue
Trivia
- The original EXE accepts arguments. The accepted arguments are shown below:
- /inst: Install to system directory silently, without the initial payload.
- /unst: Uninstall the installation
- /ver: Show an about dialog message box with version
- According to the decompiled source code, holding down F10 when double clicking the original EXE will cause the malware to decompile itself and unpack all the assets and codes. However, this behavior is tested not working on a WinXP virtual machine.
Link
NOTE: The following application contains a screamer!
- web.archive.org/web/20041106190224/geocities.co.jp/SiliconValley-Oakland/8358/mysoft/files/madoka08.zip
- files.screamer.wiki/other/madoka08.zip
- Author's homepage: web.archive.org/web/20040806024306/geocities.co.jp:80/SiliconValley-Oakland/8358/mysoft/mysoft.html
- Showcase: youtube.com/watch?v=COIEKlgnDm4